##前言: 上一个post,我们讲了snort的安装与NIDS模式的简单测试。这一个post,博主会介绍如何正式地启用snort,并借此进行网络入侵的检测。
##搭建环境:
### Ubuntu 16.04 (注意:不同的系统会对snort的安装有影响)
### Snort 2.9.15 (博主安装于2019年10月,过后可能会有新版本)
##1. PulledPork安装(用于自动更新snort的规则)
// 安装依赖 sudo apt-get install -y libcrypt-ssleay-perl liblwp-useragent-determined-perl // 下载安装最新的PulledPork cd ~/snort_src wget https://github.com/shirkdog/pulledpork/archive/master.tar.gz -O pulledpork-master.tar.gz tar xzvf pulledpork-master.tar.gz cd pulledpork-master/ sudo cp pulledpork.pl /usr/local/bin sudo chmod +x /usr/local/bin/pulledpork.pl sudo cp etc/*.conf /etc/snort // 测试是否安装成功 /usr/local/bin/pulledpork.pl -V
##2. 配置PulledPork
// 编辑PulledPork的配置文件 sudo vi /etc/snort/pulledpork.conf // 按照下述修改: Line 19: 输入您的 oinkcode (如果没有,请注释掉本行) Line 29: Un-comment for Emerging threats ruleset (not tested with this guide) Line 74: change to: rule_path=/etc/snort/rules/snort.rules Line 89: change to: local_rules=/etc/snort/rules/local.rules Line 92: change to: sid_msg=/etc/snort/sid-msg.map Line 96: change to: sid_msg_version=2 Line 119: change to: config_path=/etc/snort/snort.conf Line 133: change to: distro=Ubuntu-12-04 Line 141: change to: black_list=/etc/snort/rules/iplists/black_list.rules Line 150: change to: IPRVersion=/etc/snort/rules/iplists // 首次运行测试 sudo /usr/local/bin/pulledpork.pl -c /etc/snort/pulledpork.conf -l
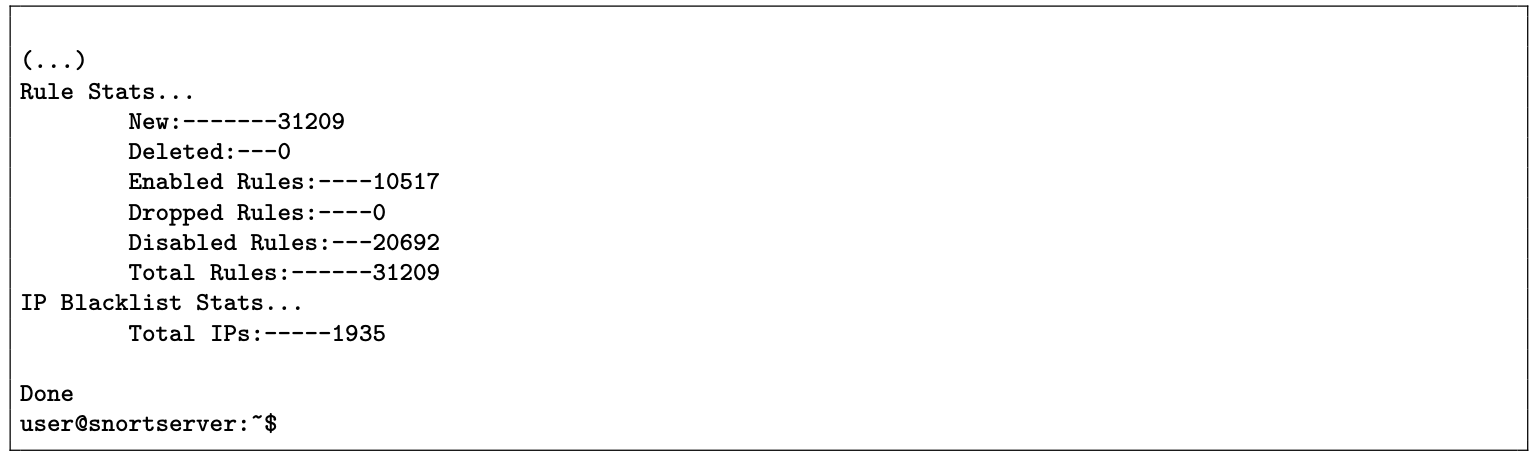
**如果出现下述情况,说明配置成功(这里warning不需理会)
##3. 配置snort,使其配合PulledPork运行
// 编辑snort的配置文件 vi /etc/snort/snort.conf include $RULE_PATH/snort.rules // 加在最后一行 // 测试规则配置是否成功 sudo snort -T -c /etc/snort/snort.conf -i ens3 // 使PulledPork每日运行 sudo crontab -e 01 04 * * * /usr/local/bin/pulledpork.pl -c /etc/snort/pulledpork.conf -l // 加在空白处
##4. 创建自动运行脚本
sudo vi /lib/systemd/system/snort.service // 加入以下内容(注意:格式必须保持一致) [Unit] Description=Snort NIDS Daemon After=syslog.target network.target [Service] Type=simple ExecStart=/usr/local/bin/snort -q -u snort -g snort -c /etc/snort/snort.conf -i ens160 [Install] WantedBy=multi-user.target // 启用脚本 sudo systemctl enable snort sudo systemctl start snort // 查看运行状态 systemctl status snort
##5. 查看检测结果
vi /var/log/snort/alert